In this blog, we explore the origins of DNSSEC, explain how it works at a high level, and examine the key challenges that have slowed its adoption. We also break down the main pros and cons of DNSSEC to help you decide whether implementing it is the right move for your organisation.
A Quick Introduction to DNSSEC
DNSSEC (Domain Name System Security Extensions) is a technology that provides an additional layer of security to the Domain Name System (DNS) by adding digital signatures to DNS data. DNS is responsible for translating human-readable domain names, such as example.com, into IP addresses that computers use to identify each other on the internet.
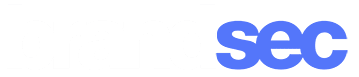
With DNSSEC, digital signatures are added to DNS records, allowing DNS resolvers to verify that the information they receive from a DNS server is authentic and hasn’t been modified in transit. This helps prevent attackers from intercepting DNS queries and returning incorrect IP addresses that lead users to malicious websites, a tactic known as DNS spoofing or DNS cache poisoning.
How Does DNSSEC Work?
DNSSEC works by adding digital signatures to DNS data, starting from the root zone of the DNS hierarchy down to the individual domain names. These signatures are generated using public-key cryptography.
When a client requests a DNS resolution, the DNS resolver requests the necessary DNS data from the authoritative name server of the domain. With DNSSEC, the authoritative name server provides not only the requested DNS data, but also a digital signature of the data.
The digital signature is created using the private key of the zone’s DNSSEC key pair, which is kept securely with the zone administrator. The public key is published in the DNS, allowing anyone to verify the digital signatures of the DNS data using the public key.
The DNS resolver then uses the public key to validate the digital signature of the DNS data. If the digital signature is valid, the resolver knows that the DNS data has not been tampered with and can be trusted. By providing a chain of trust from the root zone to the individual domain names, DNSSEC helps prevent DNS spoofing and other types of DNS attacks.

Enterprise DNS Management Smart DNS Management, Backed by Experts
Learn about our Managed DNS service for the best uptime, faster performance, and built-in security—backed by our expert team.
Background of DNSSEC: Fixing a major design flaw
In the early days of the internet, little attention was paid to security vulnerabilities. It wasn’t until internet security researcher Dan Kaminsky discovered a serious design flaw in the DNS protocol that significant efforts were made to address these issues. Kaminsky’s discovery exposed a shortcoming in the DNS protocol that allowed attackers to launch cache poisoning attacks against the lookup side of the DNS, putting users’ digital safety at risk.
Thanks to Kaminsky’s efforts, the DNS technical community began to take steps to improve the security of the DNS. In 2008, ICANN signed the root zone for the first time, representing a significant milestone for DNSSEC. In 2018, the root zone’s key signing key was successfully updated for the first time, further strengthening the security of the DNS.
However, the importance of DNSSEC was highlighted by a series of international DNS hijacking campaigns in 2018 and 2019. These attacks prompted the United States Cybersecurity and Infrastructure Security Agency (US-CERT) to issue its first-ever Emergency Directive, calling on all DNS stakeholders to fully deploy DNSSEC.
Moving forward, ICANN is committed to promoting the use of DNSSEC to ensure the security and integrity of the DNS. The organization will continue to encourage ccTLDs that have not yet signed their zones to do so, and will urge DNS resolver operators to enable DNSSEC validation to prevent DNS attacks. Thanks to the efforts of Kaminsky and other internet security researchers, the online world is becoming a safer place for users around the globe.
DNSSEC Adoption has been slow
Geoff Huston in a 2024 APNIC blog titled “calling time on DNSSEC” argued that, after nearly 30 years of development, DNSSEC remains stalled in partial adoption, with low domain-level uptake and inconsistent resolver validation. He highlights persistent barriers—such as lack of awareness, tool and automation shortcomings, complexity, and weak economic motivation—that prevent DNSSEC from gaining meaningful traction, despite its theoretical benefits.
As someone working with brands to secure their digital infrastructure, I’ve seen firsthand how DNSSEC rarely features in security conversations—even among technically mature organisations. It’s not that the benefits are in doubt, but rather that the operational effort, perceived fragility, and unclear ROI make it an easy item to defer. Most businesses focus their energy on TLS, firewalls, and endpoint protection—tools with more visible outcomes—while DNSSEC remains a checkbox that few understand well enough to tick confidently. Until deployment becomes simpler and more value-driven, it’s hard to see that changing at scale.
Does Australia Support DNSSEC?
Australia’s DNS infrastructure includes full DNSSEC support at the registry level. The .au domain has been DNSSEC-signed since 2014, and auDA operates a key signing infrastructure as part of its registry services. in March 2025, auDA reaffirmed its ongoing commitment to administering a trusted .au domain, implying continued support for security capabilities including DNSSEC, as part of its core responsibilities.
However, actual adoption within Australia remains low. While the infrastructure exists, few second-level domains (such as .com.au) are signed with DNSSEC, and only an estimated 16% of Australian users are behind resolvers that validate DNSSEC responses—well below the global average of around 30%. This reflects a broader trend of DNSSEC underutilisation, where the perceived complexity and limited awareness continue to hold back broader deployment despite its security benefits

What the Pros of DNSSEC ?
DNS is core to internet infrastructure, but it was never built with security in mind. DNSSEC adds a layer of cryptographic verification to ensure DNS responses haven’t been tampered with. For tech teams, the question is whether the added complexity is worth the gain. Below, we outline the key advantages to help you decide if DNSSEC fits your environment.

Authentication: DNSSEC signs DNS responses, allowing systems to verify that data comes from the right source and hasn’t been altered. This prevents forged responses that redirect users to malicious sites.

Security: It protects against DNS spoofing, cache poisoning, and man-in-the-middle attacks by requiring validation of signed responses, stopping attackers from injecting false data.

Trust: DNSSEC reinforces trust in DNS by ensuring data integrity, which is especially critical for banks, healthcare, and large enterprises relying on secure domain communication.

Privacy: Though not a privacy tool by design, DNSSEC limits opportunities for tampering and surveillance. Paired with DoH or DoT, it contributes to a more secure, private DNS layer.
What the Cons of DNSSEC ?
But it comes with its challenges. While DNSSEC strengthens DNS security, it comes with trade-offs that can’t be ignored. Implementation and maintenance require a level of operational maturity, and not all environments are ready for the added complexity. Below are some of the key drawbacks to consider before rolling out DNSSEC in your infrastructure.

Implementation: Deploying DNSSEC isn’t a plug-and-play task. It involves key generation, signing zones, and configuring resolvers correctly. Without in-house DNS expertise or automation tools, implementation can be timely and error-prone.

Compatibility: Despite being around for years, DNSSEC adoption (especially in remains uneven. Some resolvers, DNS services, and legacy applications may not fully support it, potentially leading to resolution failures or inconsistent behaviour.

Management: Once live, DNSSEC introduces operational overhead. Keys must be rotated securely, zones re-signed regularly, and failure scenarios handled carefully—especially during key rollover events.

Performance: Signed DNS responses are larger and can introduce slight latency. While negligible for most users, the added load may matter in high-performance or latency-sensitive environments.
Implementation Considerations
The implementation of DNSSEC involves several planning considerations such as assessing the impact on network performance, ensuring compatibility with existing DNS servers and clients, and managing key generation, storage, and distribution. While DNSSEC offers many benefits, such as improved security and trustworthiness of DNS data, it also has some drawbacks, such as increased complexity and management overhead. Despite these challenges, DNSSEC remains an important security measure for organizations that rely on DNS to provide critical services to their users.
About brandsec
brandsec is a team of highly experienced domain name management and online brand protection experts. We provide corporate domain name management and brand enforcement services, helping brands eliminate phishing platforms across the internet. Supporting some of the largest brands in the region, we offer innovative solutions to combat threats across multiple industries.

Edward Seaford
Product & Enforcement Director
Ed brings over two decades of experience in domain management, brand protection, and phishing defence. At Brandsec and Unphish, he drives the technology and partnerships while leading with a people-first approach.