The Role of Domains in Banking Login Scams
The Role of Domains in Banking Login Scams: Lessons for the next new gTLD round
Banks have spent years educating...
2025: How Scams Target Higher Education, Universities and Students
2025: How Scams Target Higher Education, Universities and Students
Australia’s university sector is one of the country’s most valuable industries, contributing more than $25 billion a year to the economy....
ASD Report: Cyber Threat Landscape 2023–24
ASD's Cyber Threat Landscape 2023–24: Introduction
The Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC) is the Australian Government’s technical authority on cyber security....
Protect Your Brand from Job Scams
Fake job scam are one the rise. Learn how to safeguard your brand against job scams with proactive monitoring and protection strategies.
Identifying and Protecting Against Scam Websites
Identify scam websites and protect your brand with brandsec’s monitoring, auditing, and takedown services. Ensure your online safety today.
Can You Report a Fake Website?
Learn how to report a fake website to Domain Name Registrars, Web Hosts, and Google for delisting.
Unphish Beta Launch
brandsec is pleased to announce the launch of Unphish beta which will see us testing our proprietary enforcement workflows with over 200 different platforms.
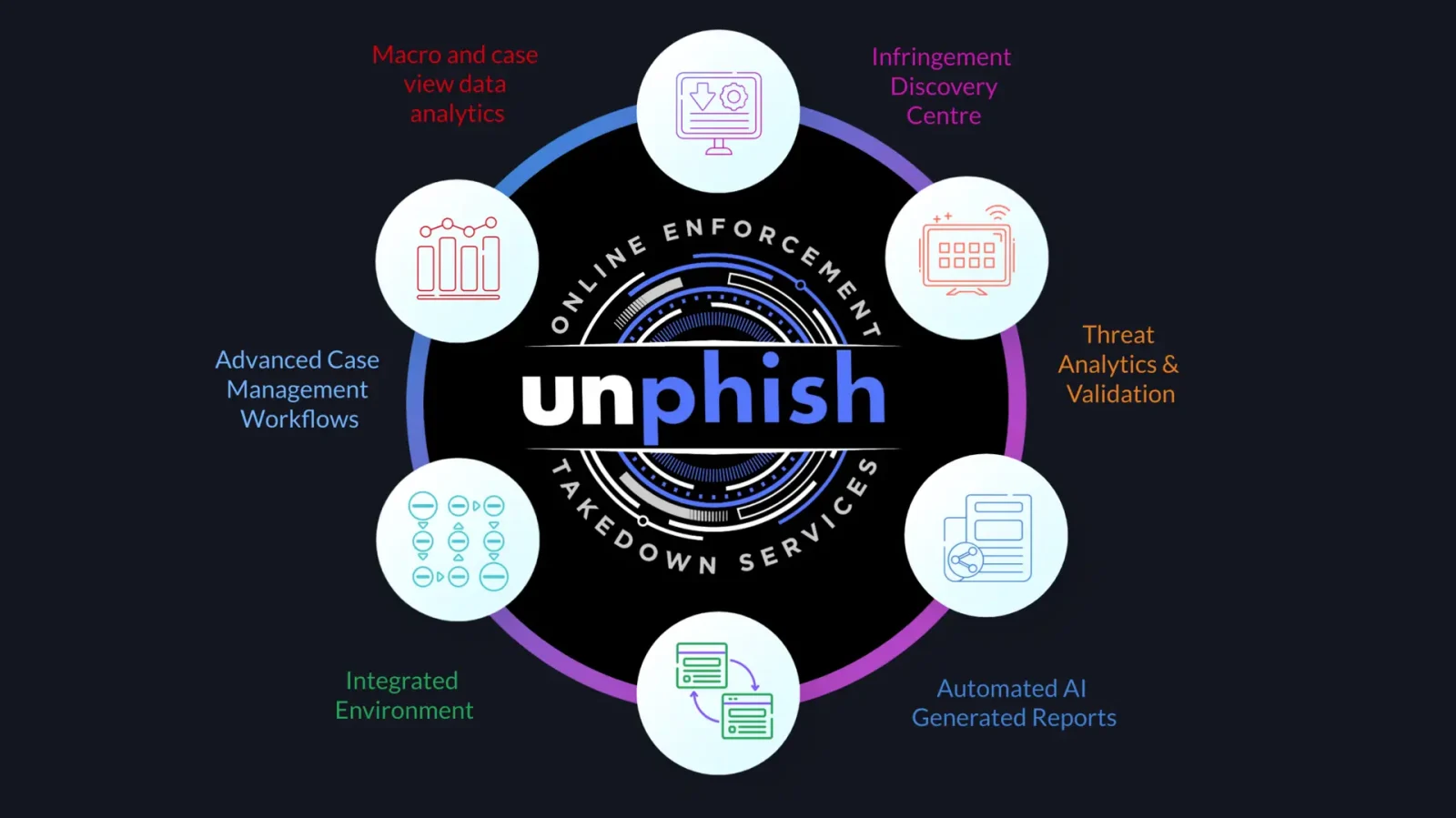
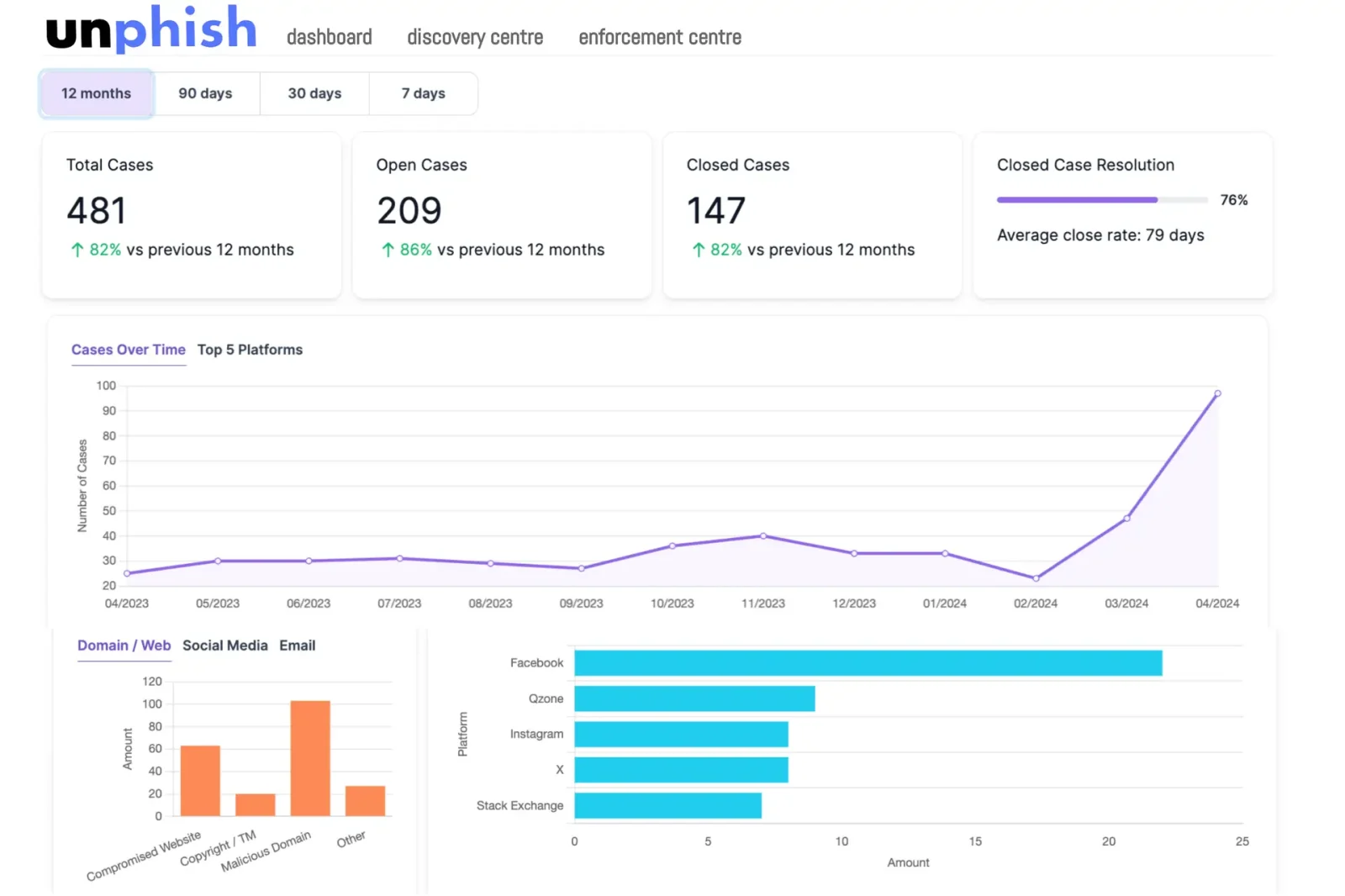
Unphish: a smart online enforcement and takedown platform
Unphish is an is an advanced online enforcement case management platform designed to empower brands to identify, report, and manage online brand infringements efficiently. Learn more here.
RAA update – Domain Name Registrars put on notice to improve their response to abuse
Effective April 5, 2024, an amendment to the 2013 Registrar Accreditation Agreement mandates new responsibilities for registrars concerning the handling of DNS Abuse for gTLD domains. This amendment specifies the obligations of registrars to act upon receiving credible...
Fake Ads on Social Media: Leads for Criminals
Fake ads on social media is a growing problem. Learn the different scams and how to defend your brands
Safe Harbor: Implications for Hosting Providers that Ignore Malicious Content
safe harbor protects hosting parties from liability associated with 3rd parties publishing content on their servers, but this protection is not absoloute.
Registrars Responsibility to Address Phishing Domains
Phishing domain names
A phishing domain name is a domain name that is registered to look like a legitimate domain name. Phishing domain names are used in phishing attacks, which are attempts to trick people into revealing personal information, such as passwords or credit card...